As cyberthreats become more sophisticated, so must our defenses. This article explores seven innovative encryption techniques that go far beyond traditional data protection methods. From homomorphic encryption to quantum-resistant algorithms, discover how these next-gen solutions are reshaping the future of cybersecurity and why it’s time to rethink your encryption strategy. 1. Homomorphic encryption: Computing without […]
7 breakthrough techniques transforming data protection
Stop replacing, start maintaining: Tips for business hardware longevity

Reliable technology isn’t just helpful; it’s essential. But constantly replacing equipment can strain your budget. The good news? With a few smart habits and a little effort, you can extend the life of your computers and hardware, keeping them running like new for longer. Give your devices the treatment they deserve Dust, fingerprints, and crumbs […]
Increasing business efficiency with Microsoft 365 Copilot AI agents

AI (artificial intelligence) has come a long way from its early days of powering chatbots and automated emails. With Microsoft’s new Copilot Studio, the evolution continues through AI agents designed to function as digital coworkers that proactively manage tasks and offer smart solutions. This article explains how it works and why it matters for businesses. […]
Building a private cloud? Here’s what usually goes wrong

Thinking about building your own private cloud? It can be a smart move for control and security, but the road isn’t always easy. From poor planning to inadequate security, small missteps can lead to big problems. In this article, we break down the most common private cloud deployment mistakes and how to avoid them. Underestimating […]
The rise of AI in employee monitoring

Monitoring software powered by artificial intelligence (AI), also known as bossware, is changing how employers track employee performance and determine actions related to employee status, such as promotion or termination. While this data-centric approach may appeal to employers, it also raises questions about fairness and the dangers of digital micromanagement. Tracking beyond time metrics According […]
Vishing: What Makes Voice Phishing So Effectively Dangerous?

Phishing is the buzzword in everyone’s mouth. As the most common method of cyber-threat, it’s a way of playing on victims’ emotions to coerce them into disclosing sensitive data.
While over 90% of cyberattacks begin with a phishing email, that is not the only way that phishers reach out to their victims. Since our digital messages have expanded far beyond our electronic inboxes, so too have phishers found other avenues for reaching out to victims and extorting money and personal information from them.
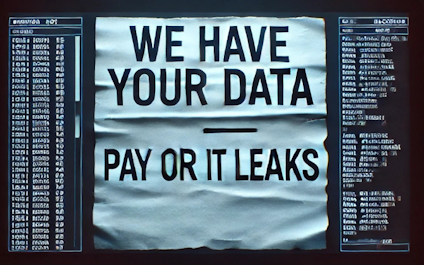
Ransomware: Past, Present and Future
10 Developer habits that can stop software attacks

A new study reveals that cybersecurity checklists often fall short when it comes to preventing real-world software hacks. But don’t fret. In this article, we explore in detail 10 practical steps developers can take to protect code and safeguard users. Limit access based on roles Not everyone needs access to every part of a system. […]
The Dark Side Of Chatbots: Who’s Really Listening To Your Conversations?

Chatbots like ChatGPT, Gemini, Microsoft Copilot and the recently released DeepSeek have revolutionized how we interact with technology, offering assistance with almost every task imaginable — from drafting e-mails and generating content to writing your grocery list while keeping it within your budget.
But as these AI-driven tools weave themselves into our daily routines, questions about data privacy and security are becoming harder to ignore. What exactly happens to the information you share with these bots, and what risks are you unwittingly exposing yourself to?