Convenience reigns supreme in the digital age, and password autofill is a major part of that. But what many people don’t realize is that using this feature can actually put their personal data at risk. By understanding why password autofill is so dangerous, you can take steps to safeguard your sensitive information from malicious hackers. […]
- Sales & Support: (877) 744-8722
- Join Meeting
- Customer Login
Spam? Don’t Just Click “Delete”
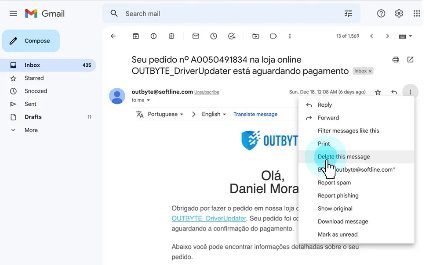
No matter what email platform you use, who you connect with, and where you choose to give out your email address, we all deal with it: Spam messages.
Sometimes, spam is clearly recognizable as fake. Others look like viable sales pitches…and sometimes they’re disguised as phishing messages to make you think that you’re interacting with something or someone that you’re not.
What is PKI and Why Does it Matter?

Do you know what a network security key is? Simply put, it’s the password that you need to input before your local network will allow you to connect. Think about your home network: Is there a special WiFi for everyone to use on the premises, and it’s locked so that the network isn’t flooded with passersby?
What You Need to Know About Physically Securing Your Devices

A lot of cybersecurity awareness revolves around the digital security of all your devices…but how well do you take care of their physical security?
Data breaches don’t just happen when your computer gets infected with malware or you fall for a phishing scam. How often have you done the “phone, keys, wallet” check before you leave a venue? Thieves can steal your laptop out of your bag or your phone from your pocket, too. Then, they can crack your password and steal all your data directly!
How Encryption Really Works: A Beginner’s Guide

Encryption is one of the most commonly misunderstood subjects when it comes to protecting sensitive data. Even those with a basic understanding of encryption often misidentify certain components, use the wrong algorithm and fail to understand how they are used in practice. These myths and misunderstandings are not only frustrating—they can also put your personal security at risk.
Roaming Mantis: Real-Time Case Study in Compromised Public WiFi

The longer you go without being negatively impacted by a data breach, it’s natural to become more blasé with some of the routine steps you take to secure your devices. For example, we all use public WiFi when we’re out of the house to quickly look something up, even though we know it’s not as safe as using our locked, private home network.
How to Manage Third-Party Risks
Breach on GoDaddy Goes Back “Multiple Years”
The ultimate guide to building an effective cybersecurity strategy
Regardless of the size of your organization, you possess a significant volume of sensitive data that cybercriminals can exploit. In the event that this data falls into the wrong hands, it can result in the loss of critical information and severely damage your reputation. This article will provide guidance on establishing a cybersecurity plan based […]



